 Advanced hardware hacking training is back at Black Hat USA this summer in Las Vegas, NV. Colin O’Flynn, creator of the ChipWhisperer project, is running two in-person training sessions in August 2023.
Advanced hardware hacking training is back at Black Hat USA this summer in Las Vegas, NV. Colin O’Flynn, creator of the ChipWhisperer project, is running two in-person training sessions in August 2023.
Over the two day course, you will learn how to conduct power analysis and fault injection attacks using a variety of the latest ChipWhisperer hardware, including ChipWhisperer-Husky and ChipSHOUTER-PicoEMP.
The first half of the two-day course looks at Side-Channel Power Analysis – that freaky method of extracting secret keys from embedded systems that doesn’t rely on exploits or coding errors. It can be used to read out an AES-128 key in less than 60 seconds from a standard implementation on a small microcontroller. Are your products vulnerable to such an attack? This course is loaded with hands-on examples to teach you not only about the attacks and theories, but how to apply them. This course has expanded to include additional material on the topic, including applications to ECC, and work on simple testing of cryptographic implementations.
The second part of the course focuses on Fault Injection Attacks. These attacks allow you to bypass authentication, dump memory, and recover keys from cryptographic algorithms. The updates to this course includes new techniques, including hands-on EM fault injection using the PicoEMP tool.
As this course uses mainly open-source tools and examples, attendees will be able to use the takeaways in their own training courses, for example training employees at their workplace in these techniques. Side Channel Power Analysis and Fault Attacks have never been more accessible, and testing your products has never been this inexpensive or easy.
 About the Hardware:
About the Hardware:
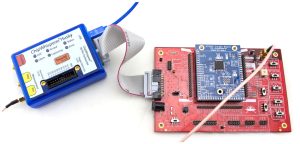
ChipWhisperer-Husky is the newest release in the ChipWhisperer line. It is designed as a compact package for working with side-channel power analysis and fault injection. It builds on NewAE Technology Inc.’s years of experience creating the ChipWhisperer-Lite and ChipWhisperer-Pro, adding new features like high-speed logic analyzers (to visualize glitches), real-time data streaming for attacking asymmetric algorithms, support for JTAG/SWD programming with an FTDI-compatible mode, and additional I/O expansion pins. ChipWhisperer-Husky is designed to be highly accessible to researchers while offering long-term support. This means that while the entire product is not OSHW-certified, the core—including the FPGA logic, microcontroller firmware, and computer code—is open-source, so you can make modifications and add features.
Released in 2022, PicoEMP is the little brother to the powerful ChipSHOUTER. This $60 USD Electromagnetic Fault Injection (EMFI) tool is designed specifically for self-study and hobbiest research. The easy-to-assemble kit brings EMFI to any undergraduate or graduate class.
Get hands-on experience using these and other ChipWhisperer capture hardware and targets at Black Hat USA this summer!
 Who is the course for?
Who is the course for?
Anyone dealing with embedded systems needs to understand the threats that can be used to break even a “perfectly secure” system (meaning no buffer overflows, ability to inject code, or other such flaws). This course assumes knowledge and experience with embedded systems, and will build upon that to teach you about the practicality of various advanced attacks on those systems.
Course Dates: August 5-6, 2023 and August 7-8, 2023.
Sign up here: Advanced Hardware Hacking: Power Analysis & Fault Injection with the ChipWhisperer. Early bird pricing ends May 26, 2023.
More Learning Opportunities
All ChipWhisperer hardware works with a variety of educational resources organized into self-taught “courses”. You can see examples of these courses as part of the ChipWhisperer Project. The paid (and free) ChipWhisperer.io video series offer step-by-step instructions, and The Hardware Hacking Handbook is a great resource for getting started with embedded security (including example lab setups).
The Embedded Online Conference is taking place April 24 – 28, 2023 but signing up gives you access to all previous year’s talks for 1 year. Catch Colin O’Flynn’s talk:
Hardware Security Analysis on Soft-Core RISC-V Processors on April 28, 2023.

